What is BlueJacking?
Bluejacking refers to the sending of unsolicited messages over Bluetooth to Bluetooth-enabled devices such as mobile phones, PDAs or laptop computers.
This attack is usually harmless, and the most effective result is the surprise of the victim. The messages can be sent from within a relatively small range radius, because of the low power of the Bluetooth radio transmitters. Bluetooth has a very limited range, usually around 10 meters on mobile phones, but laptops can reach up to 100 meters with powerful Class 1 transmitters.
While usual Bluejack attacks are performed by sending vCards via the OBEX Protocol, I’m presenting a simpler approach.
The Concept
Usually, first thing to do is to scan for nearby bluetooth enabled devices. A Bluetooth device can be detected, if it’s running in a special mode called Discovarable. In this mode, the devices advertise their presence, and offer their Bluetooth address, so remote devices can open connections to them.
Part of the Bluetooth security protocol, is the authentification mechanism know as Pairing. Devices generally require pairing or prompt the owner before they allow a remote device to use any or most of their services. Some devices, such as mobile phones, usually accept OBEX business cards and notes without any pairing or prompts.
This is why the regular BlueJacking attacks use the OBEX Business card protocol.
But we can dispatch readeble messages even easier. After we have the bluetooth address of the “victim”, we can simply require pairing to the remote device, and the user will get prompt in order to allow or deny the process. When this happens , the remote device receives the name of the device that initiated the pairing sequence. In this case, it’s the name of our device.
So all we need to do , is to set a message instead of our bluetooth device name, and initate a pair request to the remote device, the “victim”.
The result is shown below:
This snapshot was taken from a Windows Mobile 5.0 smartphone, that received this message during the pairing process.
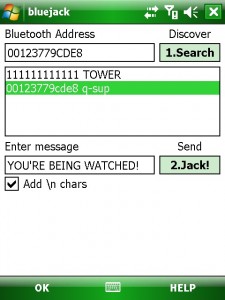
The BlueJacking was initiated from a different pocket PC device, running a simple tool:
This tool is capable of searching for remote devices that are in discoverable mode. To be subject to this attack, a device doesn’t need to be in discoverable mode, just to have the bluetooth module on, but the attacker needs to know the address.
Then the tool allows the user to define a custom message that gets set as the Bluetooth Device Name. On Windows Mobile this is achieved by setting the registry key:
HKLM\Ident\Name
Then a pair request to the remote device is transmitted using this simple bluetooth api:
BthPairRequest(&m_btaClient,4,(unsigned char *)”0000″);
m_btaClient is the “victim”‘s bluetooth address.
The tool is attached, download and use it at your own risk, as I am not to be held responsable for any damage resulting by it’s use. This article was only created to help people better understand some of the “permitted” features of the current Bluetooth implementation.
Download the tool: bluejack





Hi all!
After some experimenting, here are my findings.
Setup: HTC P3600 (Trinity) with non official WM6.1 as bluejacker, HTC Touch (Elf) with portuguese WM 5.0 as the “victim”.
On P3600, after clicking on Search, I have to double click on the name of the choosen victim device name, to make it active, even if it’s already on the “Bluetooth Adress” window. I would call it a bug… 😉
On the victim, in this particular ROM, the result is not as shown on your first image, but a notification window (like sms notification), on the bottom of the screen, with the following text (quick translation from portuguese):
“YOU’RE BEING WATCHED wishes to connect to your device by bluetooth. Do you wish to add YOU’RE BEING WATCHED to your devices list?”
And 2 buttons, “Yes” and “No”.
So, the effect is lost, altought the functionality is the same. As I understand, the notification will depend on the ROM.
But, all in all, it’s a great tool, to begin with!
Correction: HTC Touch (Elf) with portuguese WM 6.0
Thanks Vasco! Again 🙂
The double click is required to select a bluetooth address from the list.
The notification happens on all Pocket PC’s. The snapshot I’ve added is from a Smartphone.
I’ve tried to trick the notification bubble from only displaying the text, but I currently found no good way.
On smartphone the trick was to make a pair request, after naming the device MESSAGE+lots of ENTER chars. This pushes rest of the message “wants to connect to your device, etc” down and the “victim” only sees the intended message.
Try HTML. In the message put something like: YOU’RE BEING WATCHED !
Might work.
Sorry. The HTML got interpreted. It should be:
YOU’RE BEING [b]WATCHED[/b]! [br][br][br][br][br][br]
Instead of [ use < and instead of ] use >
😀 It’s full of tricks!
Did not understood the HTML sugestion, I am NOT a program developer… 😉
It works with HTML, see:

Ok, thanks for the explanation.
Now the victimm shows:
“YOU’RE BEING WATCHED!
WATCHED
YES NO”
No matter how much [br] I enter, it allways displays the second line.
By the way, I’ve noticed that BlueJack is capable of turning on the device’s bt, well done. But on 2 ocassions, the blue LED was blinking, but nothing happened, maybe bt module was off, disregarding BlueJack instructions?
And it would be nice if a changed message could be saved, instead of the default one.
And a way of clearing the list of found devices. It just keeps growing… 😛
Ok, I’ve removed the HTML instructions to make “WATCHED” bold, and I’ve got the same as in your snapshot!
Now, off to the mall, to make some victims! 😀
Hehe, ok, have fun!
BTW, does this work on the Magician?
I really liked this post. Can I copy?
Thank in advance.
Sincerely, Timur Alhimenkov.
Hello Timur, you can copy it, but only if you indicate the source (this page) and the author (me).
Thanks,
Radu
How do we uninstall this?
I can’t get my computer to recognize my device by its name. It thinks I’m “You’re being Watched”. I don’t want to connect as deviceName(You’re being watched), b/c Im afraid it will kill my partnership settings within activeSync. It also doesn’t recognize me plugged in via USB.
THoughts?
Okay, oops, you did mention the HKLM setting that holds the deviceName…so I changed it back. All is well.
Good article! I have been using Sniper from GadgeApps.net a lot and it has some quite few good features.
Sorry link was gadgetapps.net
Thanks for the info, works great!
Hi,
We have just added your latest postPocketMagic , Bluetooth BlueJacking” to our Directory of Bluetooth . You can check the inclusion of the post here . We are delighted to invite you to submit all your future posts to the directory and get a huge base of visitors to your website.
Warm Regards
This is quite a simple to do.:)
I suggest anyone who wants more to try easyjack or sman. You can get there online.
This was kinda interesting one. Simple steps can make big things, sometimes. Time to test it on my ancient SP5